When you purchase a new cloud-based system for any of your IT use cases, chances are you want to implement or continue using a centralized identity and access management tool. The fundamental idea of having these Identity Access Management (IAM) tools is to provide and maintain a single digital identity per individual inside the organization and the resources that individual has access to. All the identities and access lists of an individual can be stored and maintained in an IAM. However, your IT resources like web applications, cloud platforms, and APIs would need to talk to IAM tools to authenticate and authorize an individual to use the requested resource.
As the main idea of this approach is to maintain only one digital identity in a centralized system, IT admins can manage these identities in a centralized place with some added security features. Some of these security features can include audit logs for access events, adding or revoking access to the users, and saves users the hassle of maintaining a set of credentials in each of the systems.
How do IT resources talk to identity providers?
IT resources, like web applications, outsource user authentication steps to the IdP (Identity provider) tools. The authentication and authorization process happens in the IdP tool which communicates with the resource on whether the user was authenticated, authorized, or denied. Standards and languages such as SAML and OpenID Connect are widely used to establish a centralized federated identity.
Anypoint Platform supports integrations with any of the SAML and OpenID providers. When you integrate Anypoint Platform with either SAML or OpenID providers, users can log in to Anypoint Platform with their existing enterprise identity.
Integrating the Anypoint Platform with IdP essentially means configuring the Anypoint Platform to be able to talk to IdP to exchange information about the user authentication and authorization details. If you have a SAML-based IdP, the information exchange between the IdP and the Anypoint Platform will happen in the form of digitally signed XML documents or SAML assertion. As the Anypoint Platform supports SAML-based provider integration, it can understand and validate XML documents and act based on that. Below is a high-level diagram of how the SAML SSO process works.

Setup SSO for Anypoint Platform
Configuring SSO for the Anypoint Platform with a SAML-based IdP provider, Google Workspace (formerly known as G Suite) is nearly identical to configuring any SAML-based IdP with Anypoint Platform. Before beginning, it’s important to understand the critical aspects of configuring SAML-based SSO with the identity provider.
- Create a SAML app in Google Workspace and gather the information that uniquely identifies this app.
- Add a SAML 2.0 identity provider in Anypoint Platform and configure with the information that is obtained from the Google SAML app.
- You would then need to map the fields in both the systems to pass the data (SAML assertion) through the systems to authenticate and authorize a user.
Let’s begin! Go to your Google workspace admin console and navigate to Apps → SAML Apps → Add App → Add Custom SAML app.
When you give the name of the SAML app, the next screen shows you two options.
Step 1: Download the metadata file now. We need to use that to configure the Anypoint Platform to configure SSO. This metadata file includes information like the Issuer and the public key that uniquely identifies your SAML app in your Google Workspace. You need to use this file to configure Anypoint Platform to set up SAML SSO.
Now go to your Anypoint Platform account and navigate to Access Management → Identity Providers → Select SAML 2.0 from the dropdown.
Step 2: As shown in the below picture, select your metadata file from step #1 and use it as shown below. As soon as you select the metadata file, some of the fields will be populated and you would have to fill out a couple of other fields.
- Sign Off URL: The URL to redirect to after signing off from Anypoint Platform.
- Audience: This is an arbitrary string that identifies your Anypoint Platform account. The name that you give here needs to be configured exactly the same in Google Workspace. People typically use <org-domain>.anypoint.mulesoft.com as this field value.

Hit the Create button.
Step 4: Now go to your Google Workspace console again and go to the next step, where you need to provide these details:
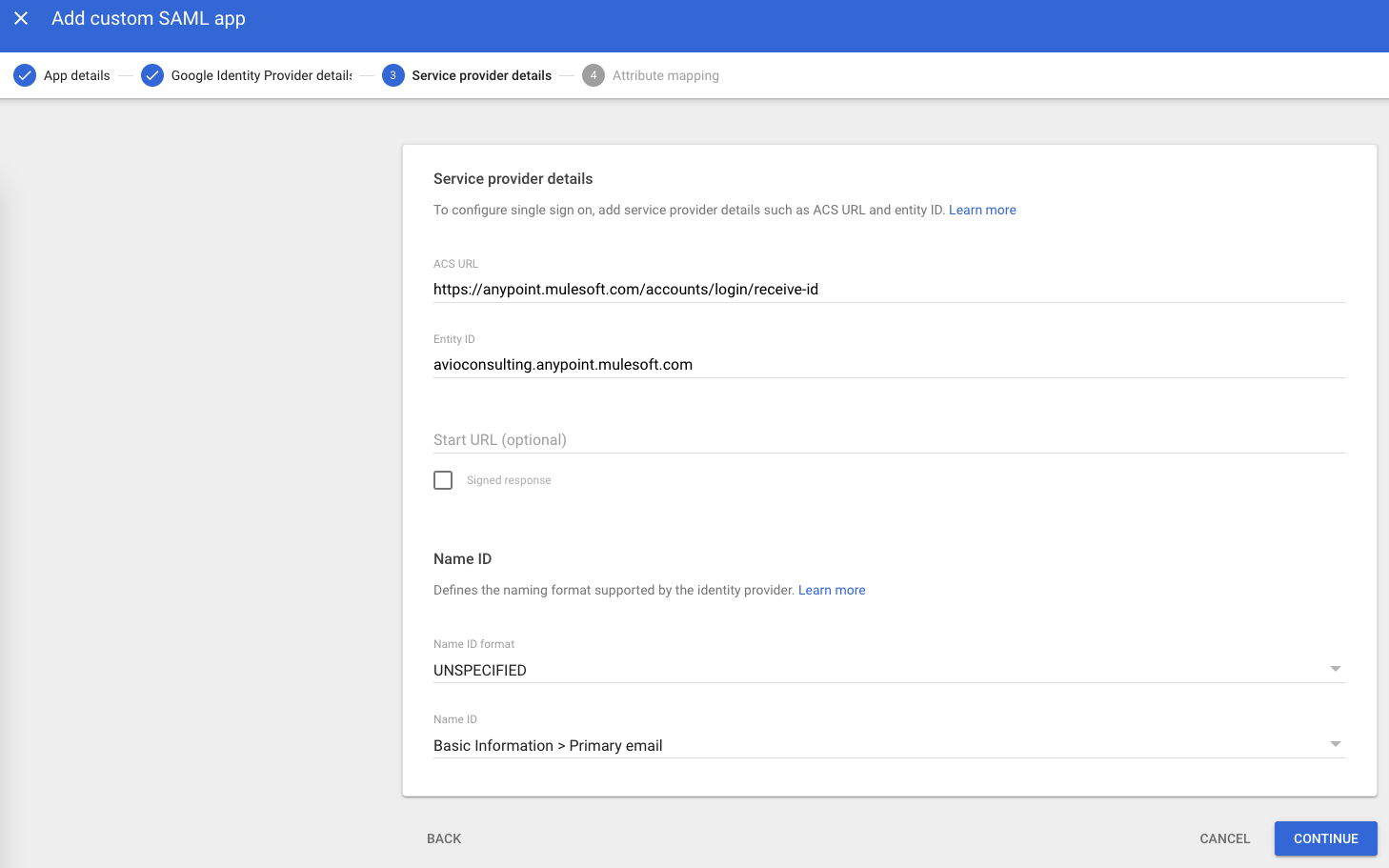
ACS URL: This is the URL for Anypoint Platform that Google Workspace sends the SAML assertion once the user is authenticated. The value for any company is https://www.mulesoft.com.
Entity ID: This is the Audience ID that we configured in the Anypoint Platform in step 2. The name must exactly match on both sides.
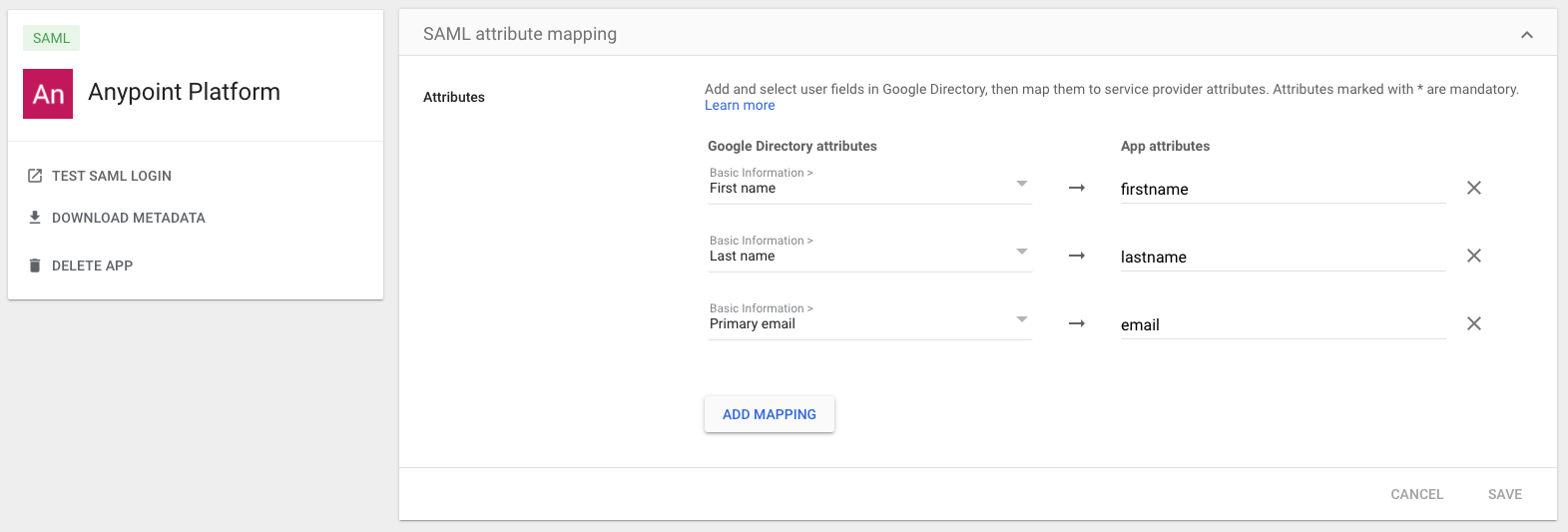
Step 5: Now you need to add SAML attribute mapping for Google to send user information in the SAML assertion payload to Anypoint Platform. When configuring SAML SSO for Anypoint Platform, you must send the email attribute from Google, otherwise, you will get an Unauthorized error. Configure the mapping like this:
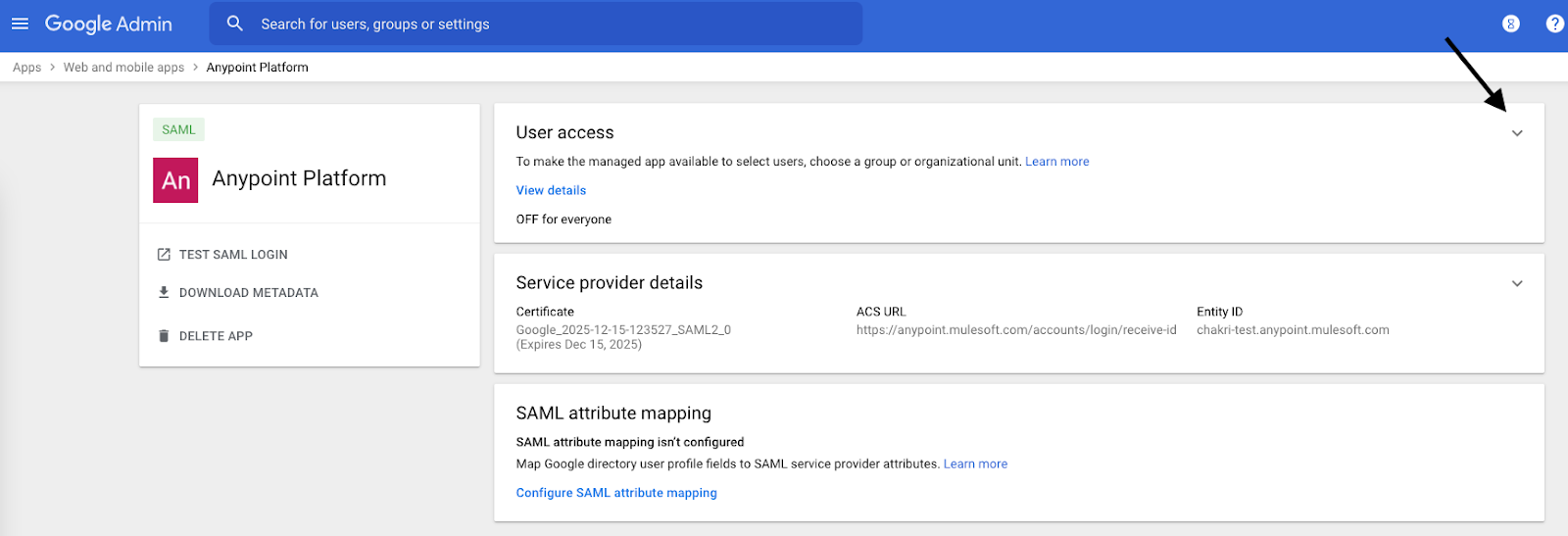
Step 6: SSO setup is almost complete! Now, we need to make this custom Google Workspace SAML app available to your Google Workspace users. Grant user access to this app as shown below.
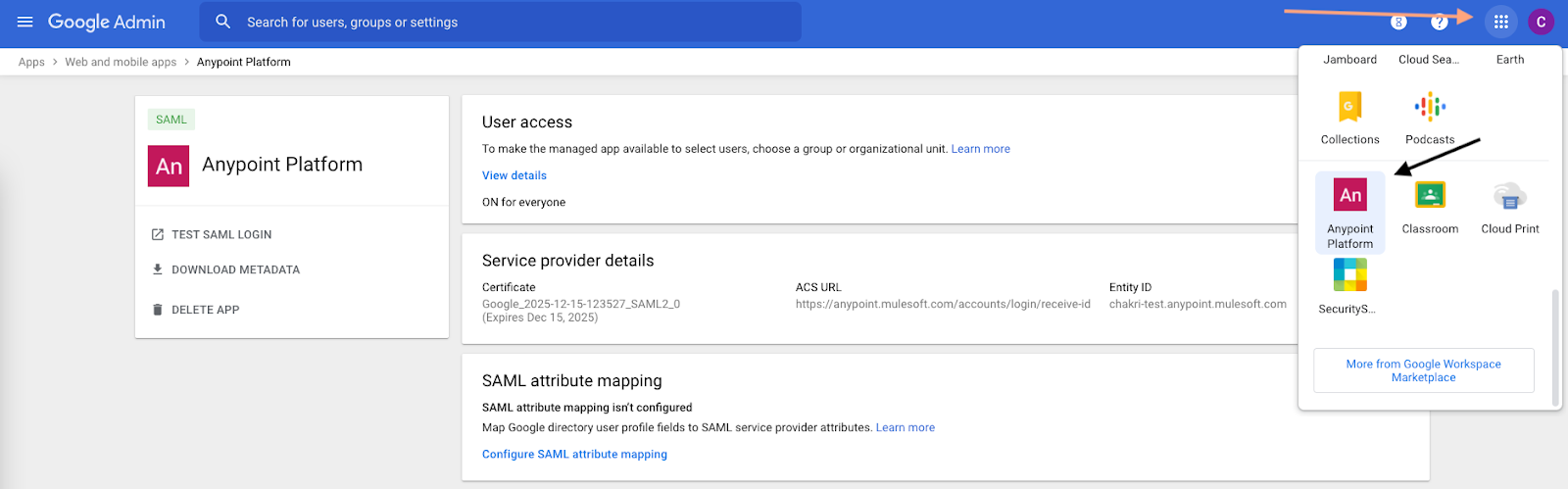
When you grant access to the users, this custom SAML app will be available to them under Google Apps:
When you click on that app, you will be taken to a page where you sign in with your Google Workspace credentials, and after successful login, you will be directed to the Anypoint Platform.
Manage Anypoint Platform Roles From Google Workspace
We successfully logged into the Anypoint Platform and now we can manage Anypoint Platform roles from the Google Workspace console. To do that we need to expose the names of the roles in Anypoint Platform so that we can send the roles fields in the SAML assertion from Google Workspace. Using these fields, Anypoint Platform will assign permissions to the user.
Step 1: Go to your identity provider settings in Anypoint Platform and provide a name for the Group Attribute.

Step 2: Set external group mapping to any of the roles in Anypoint Platform. You can create your role with a specified set of permissions and set external group mapping for it too. In the below picture, you can see the Organization Administrator role has been exposed for SAML assertions.

Step 3: Now on the Google Workspace side. We need to add a custom field to your user profile attributes so we can specify the names of the externally mapped roles from step 2 as the values of this custom field, which enables Anypoint Platform to grant permissions accordingly. Go to the Users page in Google Workspace → Manage custom attributes → Add custom attribute.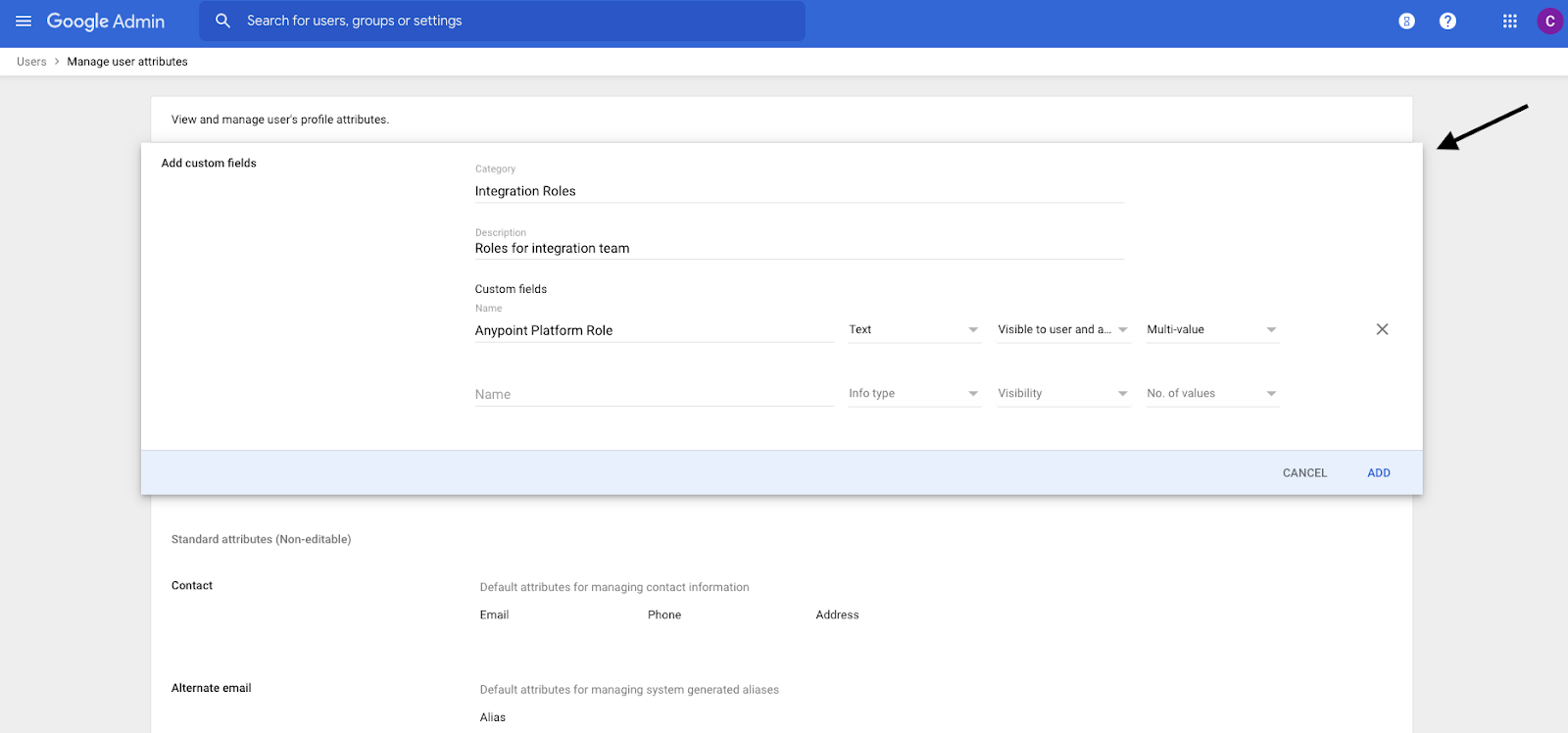
Step 4: Go to the users’ page and navigate to the user to whom you want to give the Anypoint Administrator role that we exposed in step 2 above. Then, give “admin” as the value for the newly created profile field from step 3.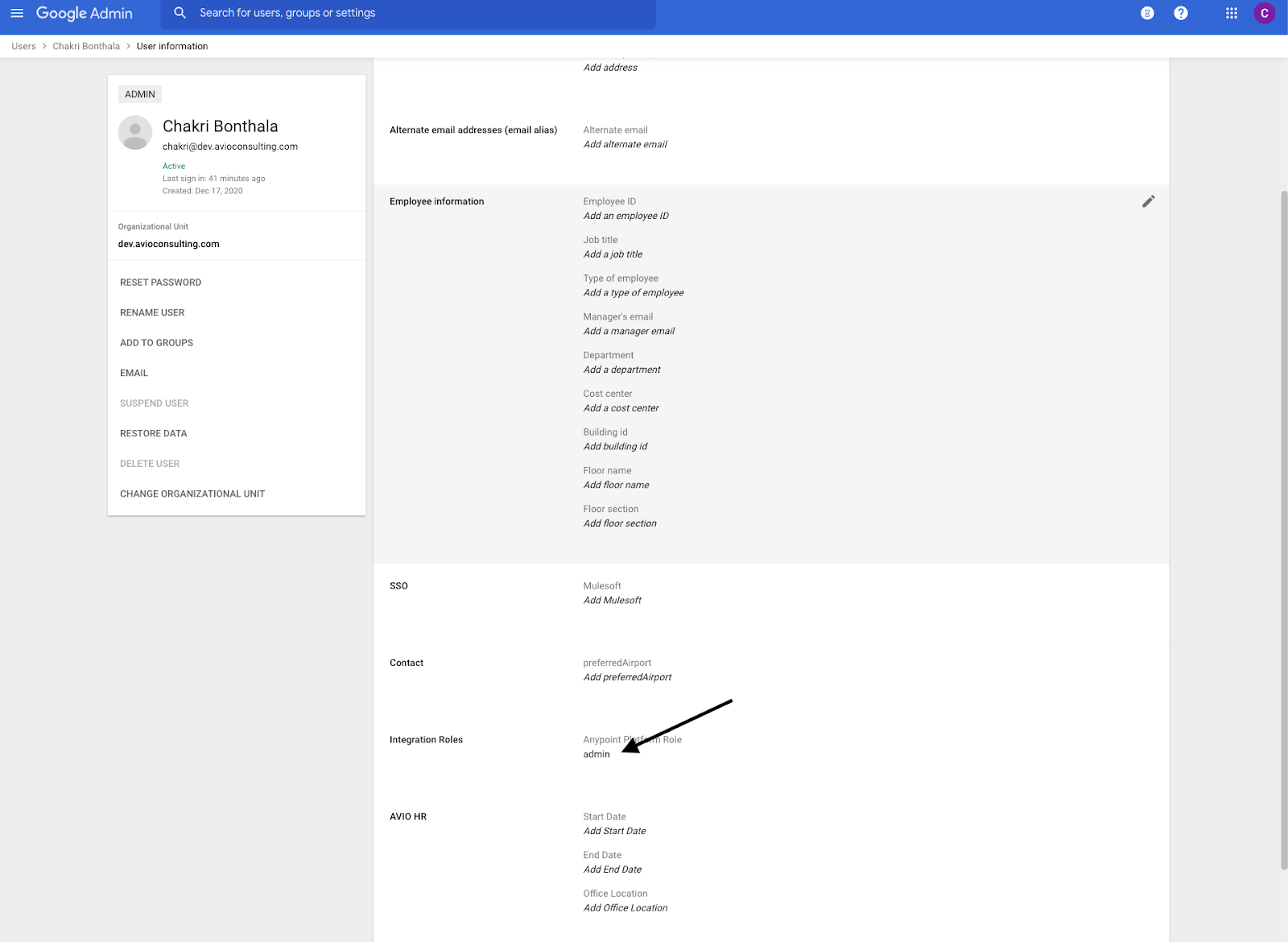
Step 5: Go to your SAML app and add one last mapping field to go into SAML assertion XML payload from Google to Anypoint Platform. Here we need to map the user profile custom attribute to the field that we specified in the Anypoint Platform identity provider config in Step 1. 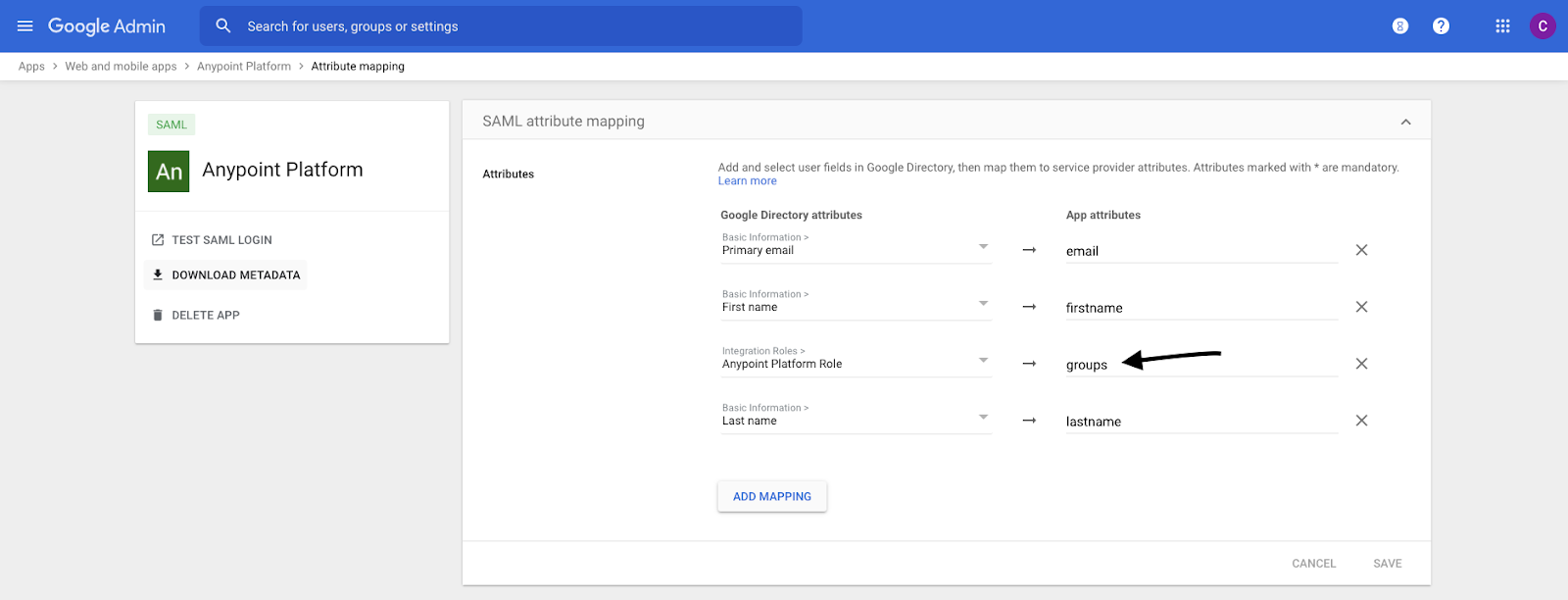
You can expose as many roles as you like in Anypoint Platform, and add those external group mapping values to your user’s custom field in Google to assign Anypoint Platform permissions. Now we are managing the users and their roles right from Google Workspace.
Note that you may need to log out and log back for the changes to take effect in the Anypoint Platform.
{{cta(‘fd5c1a6c-8547-4737-81ec-8cc8ce14246c’,’justifycenter’)}}

