Azure Key Vault is great tool for securely storing and accessing secrets. A secret could be anything that you want to control access to like passwords or API keys. A vault is a logical group of secrets that provides a secure way of accessing them.
We’ve had a few requests to create integrations that use Azure Key Vault for secret and certificate management. This allows us to dynamically retrieve secrets, keys, and certificates from Azure Key Vault without having to updating any properties within the Mulesoft application deployment. Unfortunately, there wasn’t a connector readily available. The functionality could have been done using the standard HTTP Requester, however, a connector makes the whole interaction much simpler.
So now, AVIO is happy to release the Azure Key Vault Connector for Mule 4!

Easily retrieve secrets dynamically for use inside a flow.
If you’re using Vault by HashiCorp, you can also use our Hashicorp Vault connector for Mule 4.
Our other open source connectors and tools are available through our GitHub account, such as our Custom Logger. If you have any issues or find any bugs, please report them in GitHub, and as with all open source code, please contribute.
Thanks to Manoj Amballa for help with the connector!
Version 1.1.0
In this release, we’ve included a core set of operations that helped solve the most common use cases we’ve seen. Those operations include retrieving secrets, keys, and certificates, as well as encryption and decryption. Presumably, the secret (or key, or certificate) would be loaded into the Azure Key Vault and only needs to be retrieved in the Mule flow.
- Get Secret – Retrieve runtime passwords for a database or HTTP connectors
- Get Certificate – Retrieve certificates for us in a TLS context
- Get Key – Retrieve a private key for encrypting and decrypting messages or verifying signed messages
- Encrypt – Have Azure Key Vault encrypt message contents
- Decrypt – Decrypt message content for use in Mule flows
Installing the Connector
There are a few different options for installing the connector for use. The easiest is to just use the published artifact from GitHub, however, you could also deploy it to your Exchange portal, or install it locally to try it out. See https://github.com/avioconsulting/mule-azure-key-vault-connector for other installation options.
Using the GitHub Package
The connector has been published via GitHub and is available: https://github.com/avioconsulting/mule-azure-key-vault-connector/packages/236698
To use, just add the following repository and dependency to your pom.xml
<dependency>
<groupId>com.avioconsulting.mule.connector</groupId>
<artifactId>mule-azure-key-vault-connector</artifactId>
<version>1.1.0</version>
</dependency>
. . .
<repository>
<id>github</id>
<name>AVIO Consulting GitHub Packages</name>
<url>https://maven.pkg.github.com/avioconsulting/mule-azure-key-vault-connector</url>
</repository>
Although the repository is public, as of May 2020, the package feature still requires authentication with an access token.
Creating a Personal Access Token
- Log into github.com
- Follow Github Instructions or follow to obtain personal access token
- Copy the generated token, and add it to your .m2/settings.xml file in a server block like below
- <server>
- <id>github</id>
- <username>YOUR_USERNAME_NOT_EMAIL</username>
- <password>TOKEN_CREATED_ABOVE</password>
</server>
Now, back in Anypoint Studio, refresh the pom.xml and the Azure Key Vault connector should show up in the palette.

Configuration
The next step in using the connector in your project is creating a global configuration, as shown below.

The configuration is fairly simple, only requiring:
- Azure Vault Name – Name of the vault
- Azure OAuth Base URI – The OAuth login url – for now should always be: https://login.microsoftonline.com/
- Azure Tenant ID – Tenant ID provided by Azure
- Service account Client ID
- Service account Client Secret
See official README for additional Vault Configuration options.
{{cta(‘b8ba5abd-1f2d-4416-bf68-91f04e543129′,’justifycenter’)}}
Usage
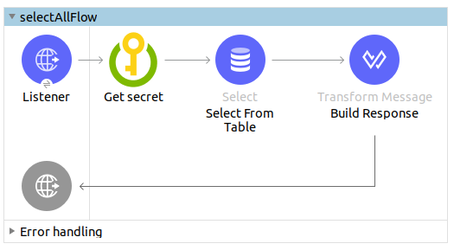
Sample Flow
In the sample below the get-secret method is used to retrieve a secret from Azure Key Vault and the response is stored in the api_secret variable. This is then used to build a HTTP body for a token request.

<sub-flow name="api_token_flow" >
<avio-core:custom-logger doc_name="Start" message="Starting"/>
<!-- get secret from azure vault -->
<akv:get-secret doc_name="Get secret - API Token Password"
config-ref="Azure_Key_Vault_Config"
secretName="api_token_password" target="api_secret"/>
<!-- Build request with api_secret response -->
<http:request method="POST" doc_name="Token Request"
path="/token" config-ref="HTTP_Request_configuration">
<http:body><![CDATA[#[%dw 2.0
output application/json
---
{
username: 'apiuser',
password: vars.api_secret.value as String
}]]]></http:body>
</http:request>
</sub-flow>
Below are additional sample calls to the key vault. The secretName/keyName/certificateName attribute’s are the name of the secret/key/certificate in Azure Key Vault.
<akv:get-secret config-ref="config" secretName="test-secret"/>
<akv:get-key config-ref="config" keyName="test-key"/>
<akv:get-certificate config-ref="config" certificateName="test-certificate"/>
Hopefully, this tool helps provide additional security in your integrations using Azure Key Vault. This is just one of the many AVIO projects, browse our GitHub account to check out some of the others and again, feel free to comment and contribute.
{{cta(‘37125fb5-39d7-4bb8-a9ec-5369a67c7655’)}}